Cybersecurity Company in Washington DC
Safeguard your business with cybersecurity solutions built to meet technological challenges in the modern workplace.
Cybersecurity Managed Services + Consulting Solutions for Business
With the escalating number and severity of malicious cyber attacks, numerous organizations will face major challenges in effectively protecting and securing end-users from potential threats and unauthorized access to corporate documents and data. However, it is crucial to strike a balance between robust business measures and maintaining employees’ productivity.
Vortex’s managed cyber security service offers a comprehensive solution that addresses both aspects. By assuming the responsibility of safeguarding your IT infrastructure around the clock, we provide 24/7 continuous monitoring of your network, systems, and data. This ensures that potential threats are promptly detected and mitigated, allowing your employees to work without disruption or concern.
Get a Free Cyber Risk Assessment
"*" indicates required fields
Our cyberSecurity Program Fundamentals
Our cybersecurity services provide an additional layer of protection for Microsoft Windows and Microsoft 365 environments, going beyond conventional security measures. With regular vulnerability assessments, penetration testing, and specialized tests, our expert team uncovers weaknesses that could expose your systems or processes to potential attacks.
These enhanced security measures form the foundation of a strong cloud data security program, ensuring the confident safeguarding of your business and critical assets against evolving cyber threats.
Dark Web Monitoring
Stay one step ahead of cybercriminals with our dark web monitoring services. We continuously scan this underground marketplace, to detect any stolen credentials or compromised information related to your business. By proactively monitoring we provide early warning and take swift action to mitigate any potential risks against your sensitive and personally identifiable data from unauthorized access.
Remote and Mobile Network Monitoring
In today’s mobile-centric work environment, securing your workforce’s network connections is crucial. Our mobile workforce network monitoring services keep track of network activities, ensuring that mobile and remote employees have secure and encrypted network connections when accessing corporate resources. By monitoring and analyzing network traffic, we identify any suspicious behavior or potential security breaches, allowing for immediate response and safeguarding your data on the go.
Conditional Access Policies
With our conditional access policies, we take advantage of Microsoft’s powerful capabilities to provide granular control over user access to your organization’s resources. By leveraging Microsoft’s conditional access features, we help you define specific criteria and requirements for accessing sensitive data, applications, or systems. By implementing these policies, you can enforce multi-factor authentication, device compliance checks, and location-based restrictions to users.
Secure Data Backup
Protect your valuable data from accidental loss, hardware failures, or malicious attacks with our secure data backup solutions. We implement robust backup strategies tailored to your business needs, ensuring regular and encrypted backups of your critical information. In the event of data loss, we offer efficient restoration processes, allowing you to quickly recover and resume operations without compromising productivity or security.
Firewall Protection
Safeguard your network from unauthorized access and malicious activities with our comprehensive firewall protection services. Our team configures and manages firewall solutions tailored to your specific requirements, creating a secure barrier between your internal network and external threats. By monitoring incoming and outgoing network traffic, we detect and block potential threats, providing you with peace of mind knowing your network is fortified.
Email Encryption
Email is one of the most common and essential communication tools for businesses. Unfortunately, this critical information channel is also a prime target for cyber threats from phishing, malware, and data breaches if not encrypted. We help train your team to identify suspicious emails and learn how to handle them through anti-phishing response strategies, spam filtering mechanisms, and a secure email gateway.
Network Security
Our network security services cover the entire spectrum of protection, from designing and implementing secure network architectures to monitoring and managing network activities. We employ industry-leading technologies and best practices to detect and prevent unauthorized access, malware infections, and other network-based threats.
Data Breach & Cyber Threat Detection
Detecting data breaches and cyber threats early is critical in minimizing damage and mitigating potential risks. Our advanced detection systems continuously monitor your network, systems, and data, leveraging sophisticated algorithms and threat intelligence. This proactive approach enables us to identify and respond swiftly to any suspicious activities, ensuring rapid containment and remediation to protect your sensitive information.
Information Governance
Establish effective information governance capabilities with Microsoft’s features to ensure the proper handling, storage, and protection of your data throughout its lifecycle. Our services include policy development, data classification, access controls, and data retention strategies. By implementing robust information governance frameworks, we help you comply with regulations, protect sensitive data, and maintain data integrity and confidentiality.
How our CYBERSECURITY Managed Services work
Our program is designed to seamlessly integrate with your existing workflows and technologies, allowing for enhanced security while keeping productivity levels high. With Vortex’s managed cyber security program, you can achieve enterprise mobility, digital security, and employee productivity, all in a harmonious balance.
We understand that vulnerabilities can exist in unexpected areas, and our thorough approach ensures that no stone is left unturned. With proactive monitoring of all devices on your network, we swiftly identify potential threats and take immediate action to mitigate attacks before they can cause significant harm.
We Manage your CyberSecurity for you
When we manage your cybersecurity program we enhance the security posture of your organization’s IT infrastructure, while providing ongoing support from our live help desk and team. Consulting and training within our managed cybersecurity and IT services ensure that your organization’s systems and processes are regularly assessed, audited, and updated to address evolving cyber threats.
We consult on cybersecurity & Compliance
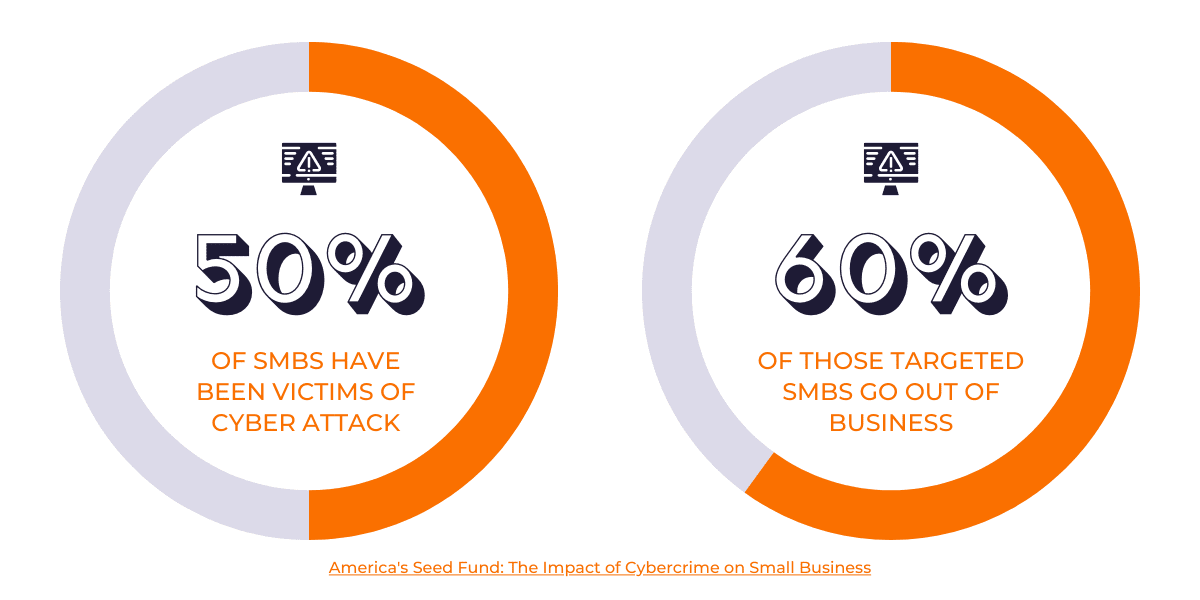
As skilled professionals in cybersecurity technologies and IT strategies, Vortex not only offers comprehensive cybersecurity consulting but also provides clients with a detailed audit and plan before implementing any recommended enhancements. With our expertise, we assess your existing security measures, identify vulnerabilities, and develop a strategic roadmap to creating a security-first culture for SMBs.
We train your IT staff on Cyber threats
Establish a culture that prioritizes security with our comprehensive cybersecurity training program. Empower your employees with the knowledge and skills necessary to identify and respond to potential cyber threats. By raising cybersecurity awareness and providing education, your employees become a valuable line of defense against malicious activities, ensuring a safer digital environment for your business.
request a Cyber threat Assessment
At Vortex, we strive to offer cost-effective cybersecurity programs tailored specifically for your business to achieve regulatory compliance and enhanced business continuity. As the significance of robust cybersecurity programs continues to grow for businesses in Washington, DC, allow us to eliminate the complications and intricacies from the equation.
Request a cyber risk assessment for a comprehensive security review that allows us to determine your existing assets, identify your requirements, and pinpoint areas where our assistance is required.